BrunoZero
@BrunoModificatoCTFer for: @Water_Paddler / Security auditor @osec_io my writeups: https://t.co/XurIhbWdj7 24y
Similar User

@0rganizers

@_MatteoRizzo

@gregxsunday

@ptrYudai

@justCatTheFish

@terjanq

@Water_Paddler

@vie_pls

@r3kapig

@zeyu2001

@0xGodson_

@S1r1u5_

@mystiz613

@maple3142

@TheGrandPew
our new look is here 🎨 we're ushering in the next chapter of HackMD with an updated logo, bold colors, and a new site. read more in our announcement below or check it out for yourself at hackmd.io bit.ly/3MlvJZZ
Las Vegas is a city where everyone begs for tips even for doing something that requires 0 effort, not sure if it's an american thing or just Las Vegas
Defcon attendees are not the "ideal las vegas clients", that spend a lot at games and walk drunk like zombies all days getting scammed all over their way.. this was my 3rd Defcon, and got to the conclusion: Vegas is too hot, too expensive, fake,generally hostile to average hacker
New job research : 1) Check how Lavamoat can protect someone from supply chain attacks 2) A bypass on lavapack And some other fun stuff :)
NEW: Supply chain attacks are increasing in popularity in Web3. Lavamoat has emerged as a robust defense mechanism - but it’s not perfect. This blog spills the beans on some sneaky bypasses, and show how tricky it is to lock down JavaScript ecosystems. osec.io/blog/2024-06-1…
New blog! This time a high severity session takeover in Zoom worth $15,000. Read the story of how @sudhanshur705 , @BrunoModificato and I chained 2 completely useless XSS vulns to steal OAuth tokens, hijack browser permissions, and more: nokline.github.io/bugbounty/2024…
I think it's time for a solution ⏰ TL;DR - Eventlet normalizes - to _ in header keys. - The Fetch spec blocks Transfer-Encoding but not Transfer_Encoding. - Bypass tracking policy on Firefox using open(). Detailed writeup 👇 mizu.re/post/twitter-e… 1/2
Small Challenge Time 🚩 Rules 📜 - You should display an alert containing the flag cookie :) If you find the solution, please do not send it in the comments; send me a DM instead 📩 Challenge link and sources👇 - challenges.mizu.re:33333 - challenges.mizu.re/chall_03/sourc…

Playing CTF kind of gives me anxiety and stress, I have a lot less motivation. However, I love those single good challenges on Twitter. I suggest this one :)
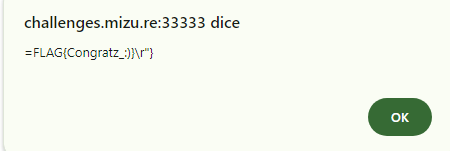
Small Challenge Time 🚩 Rules 📜 - You should display an alert containing the flag cookie :) If you find the solution, please do not send it in the comments; send me a DM instead 📩 Challenge link and sources👇 - challenges.mizu.re:33333 - challenges.mizu.re/chall_03/sourc…

I've just moved in Zurich and I'm already in love with the way of life here, I no longer miss Barcelona. And just realized how bad was living in Italy
Got a solution, even if mine probably wasn't the smartest one. I kinda like those minimalistic challenges with cool tricks. I recommend trying it.

This Friday, I'm presenting a novel technique as part of my talk "Secret web hacking knowledge - CTF authors hate these simple tricks". I've made a challenge about it, will you be able to pop an alert on pilv.ar ? The whole source code is in the screens below :)


Today I turn 24, wanted to do an introspection post for 2024 because a lot of stuff happened but I am too lazy and was also super sick. But our research post "Metamask Snaps: Playing in the Sand" has been nominated here. Please vote it (if you like it).
Nominations are now open for the top 10 new web hacking techniques of 2023! Check out the nominations so far, and make your own here -> portswigger.net/research/top-1…
It's been a while since I did technical research just to take a break for the sake of my mental health, but we recently published a research related to Metamask Snaps, including : 1) How does the Metamask sandbox work, especially on the Snap environment 2) A bug on the sandbox
Metamask Snaps: Playing in the Sand Published November 1st, 2023 osec.io/blog/2023-11-0…
🚀Exciting News! Introducing my latest work: Beyond XSS This series of articles aims to introduce front-end security topics, perfect for frontend devs and those intrigued by frontend security. Suitable for all skill levels from beginners to intermediates aszx87410.github.io/beyond-xss/en/
PSA: Web3 is plagued by the same bugs that threatened the internet over 2 decades ago. We compiled 3 case studies on how "old" bugs continue to reappear in the new era of decentralization and blockchain. Check out the deep dive here 👉🏼 osec.io/blog/2023-08-1…
Wooo woo we got second place ( team mates carry + Wtf mmm KeK). Vegas it’s also pretty weird

What does "memory-safe" actually do? Join us on an exploration into the Solidity compilation pipeline, optimization assumptions, and how it all relates to "memory-safe" assembly 🦦 osec.io/blog/2023-07-2…
This is very usefull in order to study ZK, learned a lot. I also realized I forgot almost all the high-school math😭
sunrise-clerk-234.notion.site/Hickup-s-ZK-Jo… Not a traditional reading list, but what I've personally read / watched that I felt was crucial in understanding ZK so far. Also links to handcrafted walkthroughs that hopefully help others understand better.
Sad because couldn't play Google ctf this week-end/couldn't play a lot of ctfs these weeks ----> I'm moving to a new house and country. But finally, I officially left Italy for Spain ✈️. Hope to be back playing a lot of cts and doing cool research 😄
Lost too much time on Raw Water for nothing I'm dumb
Blue Water finishes #1 in DEF CON CTF Qualifiers! 🏆 Looking forward to the finals. Congrats to all the other teams who played, and shoutout to @Nautilus_CTF for the great challenges. See you in Las Vegas!

United States Trends
- 1. #OnlyKash 58,4 B posts
- 2. Starship 197 B posts
- 3. Jaguar 63,6 B posts
- 4. Sweeney 11,9 B posts
- 5. Nancy Mace 88 B posts
- 6. Medicare and Medicaid 24,6 B posts
- 7. Jim Montgomery 4.120 posts
- 8. Jose Siri 2.875 posts
- 9. $MCADE 1.356 posts
- 10. Dr. Phil 8.564 posts
- 11. Linda McMahon 3.452 posts
- 12. Monty 11,4 B posts
- 13. Dr. Mehmet Oz 7.905 posts
- 14. Stephen Vogt N/A
- 15. #LightningStrikes N/A
- 16. Bader 4.303 posts
- 17. Cenk 14,8 B posts
- 18. Lichtman 1.268 posts
- 19. Joe Douglas 12,5 B posts
- 20. $GARY 1.920 posts
Who to follow
-
 organizers
organizers
@0rganizers -
 Matteo Rizzo
Matteo Rizzo
@_MatteoRizzo -
 Bug Bounty Reports Explained
Bug Bounty Reports Explained
@gregxsunday -
 ptr-yudai
ptr-yudai
@ptrYudai -
 justCatTheFish
justCatTheFish
@justCatTheFish -
 terjanq
terjanq
@terjanq -
 Water Paddler
Water Paddler
@Water_Paddler -
 Vie
Vie
@vie_pls -
 r3kapig
r3kapig
@r3kapig -
 Zeyu (Zayne) | @[email protected]
Zeyu (Zayne) | @[email protected]
@zeyu2001 -
 0xGodson
0xGodson
@0xGodson_ -
 s1r1us | Mohan Sri Rama Krishna Pedhapati
s1r1us | Mohan Sri Rama Krishna Pedhapati
@S1r1u5_ -
 Samuel Tang
Samuel Tang
@mystiz613 -
 maple3142
maple3142
@maple3142 -
 Pew
Pew
@TheGrandPew
Something went wrong.
Something went wrong.